End of november 2016 I took a look at the AIRTAME wireless presentation HDMI dongle's internal software and found some security issues with Firmware version 2.1.1.
Many of the configuration URLs allow unauthenticated access, even when a device control management password is set. It is possible to read out all configuration including the Wi-Fi password, overwrite all settings. Everyone may change the firmware update channel (alpha/beta/ga), start a firmware upgrade or re-enable disabled Wifi networks.
I reported the issues on 2016-11-25 and got a response 4 days later. On 2016-12-05 I got the confirmation that those issues would be fixed in the upcoming version 2.2 of the firmware.
Details
Changing settings
Everyone is able to change settings by sending parameters in the correct format to bin/save_settings.php, despite that a device control management password is set.
The reason is that /bin/save_settings.php does not check for authentication because the authentication handler is commented out:
<?php
# require_once(dirname(__FILE__) . "/authentication_handler.php");Update channel
By sending a HTTP request to bin/change_update_channel.php, you may switch the update channel to alpha/beta/ga. Unauthenticated.
Start an update
By calling bin/update.php, the update process is started. In combination with change_update_channel, this lets anyone install a new version during a running presentation. Unauthenticated.
Re-enable wifi networks
bin/disconnect.php lets one re-enable disabled wifi networks. Unauthenticated.
Diagnostics report
bin/report.php generates a zip file with diagnostics data. It contains detailled report about the device, including the password of the wifi network that the airtame is connected with (device-networks.txt -> wifi password in "psk"). Unauthenticated.
device-manager.txt in that report contains all settings that were successfully protected in bin/get_config.php.
Redirecting the dashboard
bin/launchapp.php uses the port given as parameter plus the IP address from the requestor, and uses that as HTTP URL as dashboard content.
This lets me navigate to any port on my machine, on which I can run a HTTP server that redirects the airtame to a Donald Trump video page. Unauthenticated.
Sending diagnostics
Calling bin/send_diagnostics.php lets anyone send the report to Airtame Inc.
More
There are more unprotected admin scripts, but those listed above are the ones people can do the most interesting things with
Terms of Services
The Airtame Terms Of Services define the HDMI dongle ("product") as being part of their "services".
These Terms of Service [...] governs your access to and use of our Website, mobile application, Platform, Product, software, and services (collectively, the “Services”), and any Content.
When inspecting the Airtame's code, I broke their ToS which flat out did not allow some parts of my work (5.2) or require written permission for others (5.3).
5.2 Tampering.
You may not use the Services in a way that is detrimental to the operation of the Services or the access or use of the Services by anyone else. You will not upload or transmit viruses, worms or any other destructive code. The restriction in this Section 3(f)(ii) applies to any use that interferes or attempts to interfere with the normal operations of the Services, including by hacking, deleting, augmenting or altering the Services or any Content.
I found an issue that lets the dashboard display content from my own machine, which I see as "alterting any Content".
5.3 Permission Required.
You may not, without Airtame’s prior written permission
- copy, distribute, modify, enhance, translate, reproduce, sell, resell, sublicense, rent, lease, or otherwise attempt to exploit the Services;
- decompile, disassemble, reverse engineer, or otherwise attempt to discover the source code;
- make derivative works of the Services; or
- modify another website so as to falsely imply that it is associated with the Services, Airtame or any other Airtame products or services.
Since I used SSH to access the HDMI dongle and copied the php files to my machine, I'm violating 5.3 section B. Section A was also violated because I exploited security issues during my research.
This is not hacker-friendly at all. To be legally secure, I should have nobody telling about the issues. Airtame should really change their ToS.
And I do not own the dongle because I cannot do everything I want with it. Very sad.
Fin
The airtame forum has a small discussion about this and other security problems.
Others
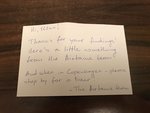
Utku Sen found more vulnerabilities and reported them to Airtame. They will be disclosed when their 3.0.0 software is out. He got a "thank you" package from Airtame:
Handwritten thank you note and a team photo are better than all kind of bounties! Thanks @airtame