I recently stumbled over Lightmeter,
a tool that is supposed to help running your own mail server by
monitoring delivery problems.
It was published in version 1.0, so I thought I'd give it a try.
Installation
Since Debian has
no package for it yet,
and I did not want to install the whole Go compilation chain on the server,
I downloaded the Control Center v1.0.1 binary for amd64 from
the
releases page.
I wanted to the Lightmeter control center under its own user and group,
with all data in /var/lib/lightmeter:
$ mkdir /var/lib/lightmeter
$ useradd --system --home-dir /var/lib/lightmeter --groups adm --shell /usr/sbin/nologin lightmeter
$ chown lightmeter:lightmeter /var/lib/lightmeter/
Then I moved the downloaded binary into /usr/local/bin/lightmeter
and made it executable.
A systemd service file was also needed:
/etc/systemd/system/lightmeter.service
[Unit]
Description=Postfix mail monitoring
Documentation=https://gitlab.com/lightmeter/controlcenter
After=network.target
[Service]
Type=simple
ExecStart=/usr/local/bin/lightmeter -listen 127.0.0.1:10020 -watch_dir /var/log -workspace /var/lib/lightmeter
TimeoutStopSec=0
Restart=always
User=lightmeter
Group=lightmeter
WorkingDirectory=/var/lib/lightmeter
ProtectHome=yes
ReadOnlyDirectories=/
ReadWriteDirectories=-/var/lib/lightmeter
[Install]
WantedBy=multi-user.target
After writing that file, systemd needs to re-read is configuration
and the service can be started:
$ systemctl daemon-reload
$ systemctl start lightmeter
$ systemctl status lightmeter
$ journalctl -fu lightmeter
Now Lightmeter is running and not accessible from the outside,
because I use Apache for SSL-termination, proxying access to LM:
<VirtualHost *:443>
ServerName lightmeter.example.org
DocumentRoot /var/www/dummy
Header set Referrer-Policy same-origin
ProxyPass / http://localhost:10020/
ProxyPassReverse / https://localhost:10020/
SSLEngine On
SSLCertificateFile /etc/letsencrypt/live/lightmeter.example.org/fullchain.pem
SSLCertificateKeyFile /etc/letsencrypt/live/lightmeter.example.org/privkey.pem
CustomLog /var/log/apache2/system/lightmeter-access.log combined
ErrorLog /var/log/apache2/system/lightmeter-error.log
</VirtualHost>
Findings
Update 2021-06: All the problems listed here have been fixed.
Lightmeter itself is in its very early stages,
more an alpha version than 1.0.
Here is a list of some of the most serious problems I found with it:
I was pretty disappointed by that Software.
Version 1.0.1 only checks if you are on an e-mail blacklist
and shows you which domains rejected e-mails.
That's all.
The people planning and creating it seem to be more interested in
layout, new technologies and monitoring instead of .. functionality.
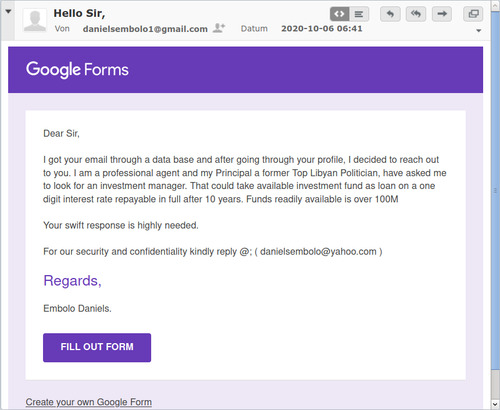
As soon as you start using it,
you send tracking data
("telemetry" in new-speak) to their servers.
They also decided to spend time on
re-implementing their frontend
instead of fixing those serious bugs and making whole software useful.
At their current development speed,
I think that Lightmeter will need two years of work until it becomes
actually useful.